Bắt đầu giao dịch
Giao dịch với hơn 200 công cụ tài chính trên toàn cầu với mức giá ổn định và chênh lệch thấp.
Exness là một sàn giao dịch Forex trực tuyến được thành lập vào năm 2008, có trụ sở tại Cộng Hoà Síp và nhiều quốc gia trên thế giới. Với hơn 15 năm kinh nghiệm trong ngành, Exness đã phát triển thành một trong những sàn giao dịch forex, CFD phổ biến và đáng tin cậy trên thế giới.
Exness cung cấp cho người dùng các công cụ và giải pháp giao dịch tốt nhất, để đảm bảo rằng các giao dịch được thực hiện với tốc độ nhanh nhất và an toàn nhất. Dưới đây là những lý do tại sao bạn nên chọn Exness:

Exness được cấp phép và quản lý bởi các cơ quan tài chính hàng đầu thế giới như: FSA, FSC, FSCA, CySEC, FCA, CMA, CBCS. Ngoài ra, Exness còn có cơ quan kiểm toán độc lập, quỹ bồi thường dành cho khách hàng. Điều này sẽ đảm bảo tính minh bạch, an toàn và bảo vệ quỹ khách hàng tốt nhất.

Exness cung cấp cho khách hàng đa dạng công cụ giao dịch, bao gồm 5 nhóm tài sản sau: Ngoại hối, hàng hóa, cổ phiếu, tiền điện tử, các chỉ số. Điều này cho phép nhà giao dịch có nhiều lựa chọn để phù hợp với chiến lược và mục tiêu đầu tư của họ.

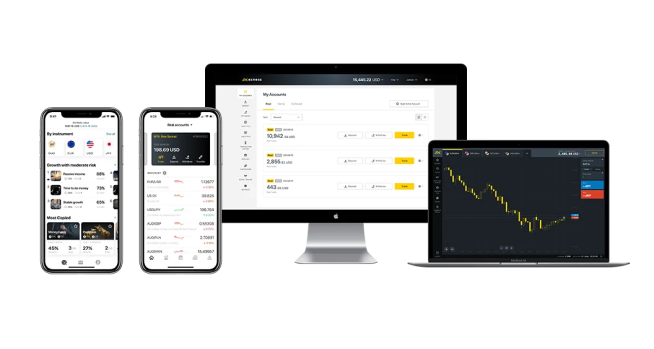
Exness cung cấp 2 nền tảng giao dịch phổ biến trên thị trường forex hiện nay đó là MetaTrader 4 (MT4), MetaTrader 5 (MT5). Đây là hai nền tảng hỗ trợ đầy đủ tính năng và công cụ, giúp nhà giao dịch thực hiện các phân tích, quản lý rủi ro và thực hiện giao dịch dễ dàng.

Exness đã xây dựng hệ thống xử lý nạp, rút tiền hoàn toàn tự động. Nhờ thế mà các giao dịch nạp tiền và rút tiền được xử lý tức thì, thậm chí khách hàng có thể giao dịch vào cả ngày thứ 7 và chủ nhật. Đặc biệt, Exness không thu bất kỳ khoản phí nạp tiền và rút tiền nào từ khách hàng.

Exness cung cấp điều kiện giao dịch linh hoạt và tốt nhất cho trader như: chênh lệch spread thấp chỉ từ 0.0 pip, phí hoa hồng cạnh tranh chỉ từ 0.2$/lot hoặc không phí hoa hồng, hỗ trợ đòn bẩy tối đa lên đến 1: vô cùng. Ngoài ra, Exness là sàn ECN nên các giao dịch sẽ được khớp lệnh nhanh chóng, đáng tin cậy và không báo giá lại.

Exness luôn đặt sự hài lòng của khách hàng lên hàng đầu. Sàn cung cấp dịch vụ hỗ trợ khách hàng 24/7 thông qua nhiều kênh liên lạc, bao gồm trò chuyện trực tiếp, điện thoại và email. Đội ngũ hỗ trợ khách hàng của Exness được đào tạo chuyên nghiệp và thân thiện, sẵn sàng giải đáp mọi thắc mắc của nhà giao dịch.
Trang web Exness được thiết kế giao diện khá trực quan và thân thiện với người dùng, nên không khó để nhà giao dịch có thể tham gia dù là người mới. Để bắt đầu giao dịch tại Exness nhà đầu tư có thể thực hiện theo các bước như sau:

Đầu tiên, hãy truy cập vào trang web chính thức của Exness, nhấn vào nút “Mở tài khoản”. Điền các thông tin theo yêu cầu, bao gồm: quốc gia, họ tên, số điện thoại/địa chỉ email, mật khẩu. Sau đó xác minh tài khoản của bạn qua Emai, số điện thoại và cung cấp giấy tờ tùy thân, ảnh chân dung của bạn.

Để nạp tiền vào tài khoản Exness, bạn chỉ cần vào khu vực cá nhân, chọn “Nạp tiền” ở bên trái màn hình, chọn một trong các phương thức thanh toán như Internet Banking, Ngân lượng, thẻ Visa/Master, ví điện tử Skrill, Neteller…rồi tiến hành làm theo các bước hướng dẫn để nạp tiền.

Sau khi nạp tiền thành công, bạn có thể giao dịch trực tiếp trên website của Exness hoặc giao dịch trên nền tảng MT4, MT5 của Exness bằng cách tải nền tảng MT4, MT5 về máy tính, điện thoại. Sau đó, đăng nhập tài khoản Exness của bạn và tham gia giao dịch.
Giao dịch với hơn 200 công cụ tài chính trên toàn cầu với mức giá ổn định và chênh lệch thấp.
Sàn Exness cung cấp hai nền tảng giao dịch phổ biến là MetaTrader 4 (MT4) và MetaTrader 5 (MT5). Đây là hai nền tảng giao dịch tài chính phổ biến, được sử dụng rộng rãi trên toàn thế giới. Đặc biệt, Exness còn có ứng dụng Exness Trade và nền tảng Exness Terminal, giúp khách hàng trải nghiệm dễ dàng hơn.




Exness cung cấp cho bạn quyền truy cập vào các công cụ phân tích kỹ thuật và phân tích cơ bản hàng đầu, để bạn có thể dự đoán biến động giá và tự tin lập kế hoạch giao dịch của mình. Các công cụ phân tích mà sàn Exness cung cấp, bao gồm: Lịch kinh tế, tín hiệu giao dịch từ Trading Central, cập nhật tin tức thị trường mới nhất từ FXStreet News,…






Exness cung cấp đa dạng công cụ giao dịch, giúp khách hàng có thể chọn ra công cụ phù hợp nhất với bản thân của mình. Dưới đây là 5 loại tài sản mà Exness đang cung cấp:

Exness cung cấp 5 loại tài khoản giao dịch khác nhau, để đáp ứng nhu cầu và mục tiêu của mọi nhà giao dịch. 5 loại tài khoản này sẽ được chia thành 2 nhóm tài khoản tiêu chuẩn và tài khoản chuyên nghiệp như sau:
Các loại tài khoản tiêu chuẩn Exness có nhiều tính năng ưu việt như: không phí hoa hồng, Spread thả nổi từ 0.3 pip, tốc độ khớp lệnh nhanh và không báo giá lại. Đặc biệt, không yêu cầu số tiền nạp tối thiểu nên phù hợp với tất cả các nhà giao dịch, kể cả người mới. Tài khoản tiêu chuẩn gồm có 2 tài khoản là tài khoản Standard và Standard Cent.
|
Loại tài khoản |
Standard |
Standard Cent |
| Tiền nạp tối thiểu | 1 USD | 1 USD |
| Đòn bẩy tối đa | 1:Không giới hạn | 1:Không giới hạn |
| Phí Spread | Từ 0.3 pip | Từ 0.3 pip |
| Phí hoa hồng | Miễn phí | Miễn phí |
| Lot tối thiểu | 0,01 | 0,01 |
| Lot tối đa | 200 | 200 |
| Cảnh báo ký quỹ | 60% | 60% |
| Khớp lệnh | Thị trường | Thị trường |
Các loại tài khoản chuyên nghiệp của Exness được thiết kế dành cho các nhà đầu tư chuyên nghiệp, giàu kinh nghiệm. Điểm nổi bật của tài khoản này chênh lệch siêu thấp hoặc thậm chí chênh lệch bằng 0, tốc độ khớp lệnh nhanh nên phù hợp với nhà giao dịch lướt sóng, nhà giao dịch trong ngày và nhà giao dịch thuật toán.
Tài khoản chuyên nghiệp gồm có 3 loại là Raw Spread, Zero, Pro. Sau đây là thông tin chi tiết về các loại tài khoản này.
| Loại tài khoản |
Raw Spread |
Zero |
Pro |
| Tiền nạp tối thiểu | 200 USD | 200 USD | 200 USD |
| Đòn bẩy tối đa | 1:Không giới hạn | 1:Không giới hạn | 1:Không giới hạn |
| Phí Spread | Từ 0.0 pip | Từ 0.0 pip | Từ 0.1 pip |
| Phí hoa hồng | $3.50 mỗi lô/ 1 chiều | $0.2 mỗi lô/ 1 chiều | Miễn phí |
| Lot tối thiểu | 0,01 | 0,01 | 0,01 |
| Lot tối đa | 200 | 200 | 200 |
| Cảnh báo ký quỹ | 30% | 30% | 30% |
| Khớp lệnh | Thị trường | Thị trường | Thị trường và tức thời |
Exness hỗ trợ khách hàng nhiều phương thức nạp tiền và rút tiền linh hoạt, an toàn và thuận tiện, bao gồm:
Hầu hết các giao dịch đều được xử lý tức thì trong vài giây, nhờ hệ thống thanh toán tự động, không cần xử lý thủ công. Đặc biệt, sàn Exness không thu bất kỳ khoản phí nạp/rút tiền nào từ khách hàng.